PWNBREW
Pwnbrew is a persistence management framework which integrates with Paterva’s Maltego to provide a tool that encompasses all phases of a red team engagement. Maltego provides an unparalleled solution for gathering and visualizing open source intelligence during the data collection phase of a security assessment.
By leveraging Maltego’s API, data from inside networks managed by Pwnbrew can also be visualized and manipulated inside the Maltego interface by way of custom Pwnbrew entities. In addition to data visualization, Pwnbrew also offers operational capabilities directly from the Maltego interface via custom local transforms.
DOWNLOAD
Version: 1.1.4.0DOWNLOAD
Release Date:
10/02/2018
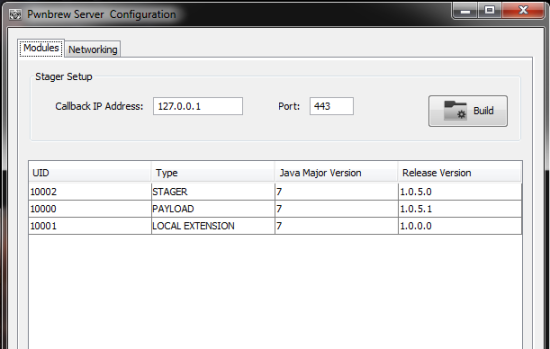
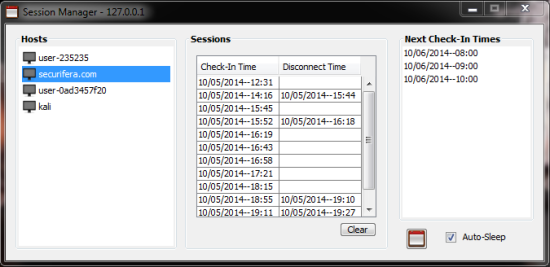
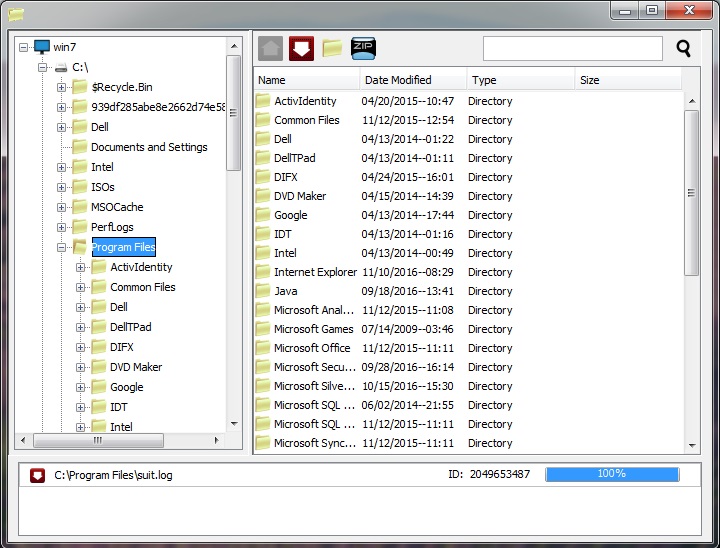
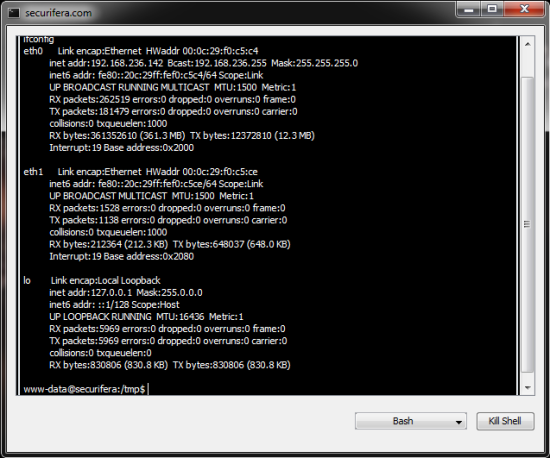
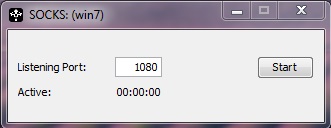
Pwnbrew is written entirely in Java. It provides an operator the ability to covertly administer systems that have been compromised during a security assessment. Presently, the Pwnbrew clients provide remote file browsing, remote command execution, and the ability to pivot commands to internal clients. In order to supplement existing pentesting technologies, Pwnbrew uses Paterva’s Maltego as the frontend GUI for managing Pwnbrew clients. It does this by way of Maltego’s API, in particular, local transforms. Pwnbrew consists of three key components to include:
Pwnbrew Server: The main backbone for all network communication and client management.
Pwnbrew Client: The remote access tool installed on compromised systems.
Maltego API Stub: The class files responsible for sending and receiving data to Maltego.
ENTITIES & TRANSFORMS
 |
Manages the connected hosts and arbitrates commands from Maltego to the hosts. |
 |
A host that is connected to a Pwnbrew Server and can be actively managed. |
 |
A host that is disconnected from a Pwnbrew Server. |
 |
A host that is disconnected from a Pwnbrew Server. |
SETUP
Post-Install
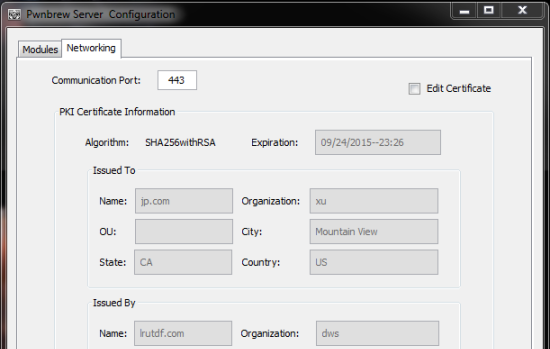
Import the certificate generated during the install into each of the Pwnbrew servers you wish Maltego to connect to.
-
- Run Pwnbrew server: java -jar Server.jar -rmp=8443
-
- At the prompt, > , enter “i” for Import SSL Certificate
-
- Enter the path to the *.der maltego certificate that is located in the install directory.