HTTP screenshots with Nmap, Chrome, and Selenium
Several months back I tweeted out a gist of a simple website screenshot python script I wrote as an attempt to fill a gap in tooling that I couldn’t seem to find anywhere. The options I was presented with were either too complex, inconsistent, or outdated. My ideal candidate would be something that integrated easily into Nmap and behaved as closely to a real browser as possible. Luckily after some research I found that selenium coupled with the chrome webdriver could provide just that.
Time and again I have been faced with a seemingly endless scope of IP addresses and a limited amount of time to review them. Whether it be a pentest, red team assessment, or bug bounty, having the ability to quickly identify targets of interest is crucial. Using Trustwave’s http-screenshot Nmap script as a template, I wrapped my python script with a Lua script and registered it with Nmap. After a few test runs against large target sets, I think it’s polished enough to release.
Setup
Given the script’s additional dependencies I assume it probably isn’t a candidate for an official Nmap repo pull request, so it’s currently hosted on my forked repo under the http_screenshot branch. After cloning the branch, the following steps will get the script operational.
Install Selenium
[sourcecode language=”bash”]pip install selenium[/sourcecode]
Download latest google chrome and install
[sourcecode language=”bash”]
wget https://dl.google.com/linux/direct/google-chrome-stable_current_amd64.deb
dpkg -i ./google-chrome-stable_current_amd64.deb[/sourcecode]
Identify google chrome version
[sourcecode language=”bash”]google-chrome –version[/sourcecode]
Go to the chrome driver download page
[sourcecode language=”bash”]google-chrome http://chromedriver.chromium.org/downloads[/sourcecode]
Download the version identified from the previous version check (Match to your version) and unzip
[sourcecode language=”bash”]
wget https://chromedriver.storage.googleapis.com/74.0.3729.169/chromedriver_linux64.zip
unzip ./chromedriver_linux64.zip[/sourcecode]
Move chromedriver to a directory in the PATH env variable or add its directory to the PATH
[sourcecode language=”bash”]mv ./chromedriver /usr/bin[/sourcecode]
Features
-
Attempts both HTTP and HTTPs protocols
-
Resolves IP address to domain as some websites render differently for IP and domain name.
-
Matches resolved domain to SSL certificate subjectName and screenshots both
Usage
The script leverages Nmap’s fingerprinting capability (-sV) to determine when it should be executed against the target. It has been added to the default set of scripts so adding -sC will execute the script if the service is determined to be HTTP. As a bonus feature, this branch also includes changes to identify HTTP services running on nonstandard ports so the default scripts will be executed against them as well. The script currently drops all screenshots in the current directory.
[sourcecode language=”bash”]
nmap -Pn -n -p443 –open -sC -sV securifera.com
Starting Nmap 7.70 ( https://nmap.org ) at 2019-06-11 11:34 EDT
Nmap scan report for securifera.com (52.4.7.15)
Host is up (0.076s latency).
PORT STATE SERVICE VERSION
443/tcp open ssl/ssl Apache httpd (SSL-only mode)
| http-screenshot:
|_ Screenshot saved.
|_http-server-header: Apache
|_http-title: 400 Bad Request
| ssl-cert: Subject: commonName=securifera.com
| Subject Alternative Name: DNS:securifera.com, DNS:www.securifera.com
| Not valid before: 2019-04-20T15:55:09
|_Not valid after: 2019-07-19T15:55:09
|_ssl-date: TLS randomness does not represent time
| tls-alpn:
| http/1.1
|_ http/1.1
[/sourcecode]
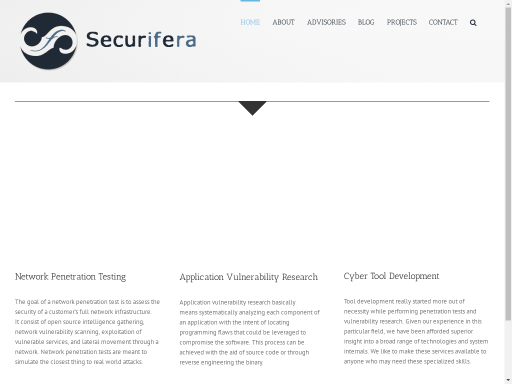
The example above should produce the following screenshot.

Have you checked out the galen framework? It’s cross-platform and can leverage the full power of selenium
Where do I download the chromedriver to? Does it go in the nmap folder? It’s not stated (only cloning the repo) but I’m assuming you need to do the normal make / make install, correct?
@John, Thanks for pointing out my missing step. You need to move the chromedriver to somewhere in the PATH env variable or add the directory you unzipped it to to the PATH.
Hey @b0yd o/
can you the repo link (404):
https://github.com/rwincey/nmap/tree/http_screenshot
Sorry I merged it in to my local master branch and forgot to update the link.